September/2021 Latest Braindump2go N10-007 Exam Dumps with PDF and VCE Free Updated Today! Following are some new N10-007 Real Exam Questions!
QUESTION 1334
A network technician has multimode fiber optic cable available in an existing IDF.
Which of the following Ethernet standards should the technician use to connect the network switch to the existing fiber?
A. 10GBaseT
B. 1000BaseT
C. 1000BaseSX
D. 1000BaseLX
Answer: A
QUESTION 1335
A wireless network was installed in a warehouse for employees to scan crates with a wireless handheld scanner. The wireless network was placed in the corner of the building near the ceiling for maximum coverage. However users in the offices adjacent lo the warehouse have noticed a large amount of signal overlap from the new network Additionally warehouse employees report difficulty connecting to the wireless network from the other side of the building; however they have no issues when they are near the antenna. Which of the following is MOST likely the cause?
A. The wireless signal is being refracted by the warehouse’s windows
B. The antenna’s power level was set too high and is overlapping
C. An omnidirectional antenna was used instead of a unidirectional antenna
D. The wireless access points are using channels from the 5GHz spectrum
Answer: A
QUESTION 1336
Which of the following technologies allows traffic to be sent through two different ISPs to increase performance?
A. Fault tolerance
B. Quality of service
C. Load balancing
D. Port aggregation
Answer: A
QUESTION 1337
A network technician is observing the behavior of an unmanaged switch when a new device is added to the network and transmits data.
Which of the following BEST describes how the switch processes this information?
A. The data is flooded out of every port. including the one on which it came in.
B. The data is flooded out of every port but only in the VLAN where it is located.
C. The data is flooded out of every port, except the one on which it came in
D. The data is flooded out of every port, excluding the VLAN where it is located
Answer: C
QUESTION 1338
There are two managed legacy switches running that cannot be replaced or upgraded. These switches do not support cryptographic functions, but they are password protected.
Which of the following should a network administrator configure to BEST prevent unauthorized access?
A. Enable a management access list
B. Disable access to unnecessary services.
C. Configure a stronger password for access
D. Disable access to remote management
E. Use an out-of-band access method.
Answer: A
QUESTION 1339
A network engineer is designing a new secure wireless network.
The engineer has been given the following requirements:
1. Must not use plaintext passwords
2. Must be certificate based
3. Must be vendor neutral
Which of the following methods should the engineer select?
A. TWP-RC4
B. CCMP-AES
C. EAP-TLS
D. WPA2
Answer: C
QUESTION 1340
A lab environment hosts Internet-facing web servers and other experimental machines, which technicians use for various tasks.
A technician installs software on one of the web servers to allow communication to the company’s file server, but it is unable to connect to it. Other machines in the building are able to retrieve files from the file server.
Which of the following is the MOST likely reason the web server cannot retrieve the files, and what should be done to resolve the problem?
A. The lab environment’s IDS is blocking the network traffic 1. The technician can whitelist the new application in the IDS
B. The lab environment is located in the DM2, and traffic to the LAN zone is denied by default. The technician can move the computer to another zone or request an exception from the administrator.
C. The lab environment has lost connectivity to the company router, and the switch needs to be rebooted. The technician can get the key to the wiring closet and manually restart the switch
D. The lab environment is currently set up with hubs instead of switches, and the requests are getting bounced back. The technician can submit a request for upgraded equipment to management.
Answer: B
QUESTION 1341
A technician is deploying a low-density wireless network and is contending with multiple types of building materials.
Which of the following wireless frequencies would allow for the LEAST signal attenuation?
A. 2.4GHz
B. 5GHz
C. 850MHz
D. 900MHZ
Answer: B
QUESTION 1342
A company that uses VoIP telephones is experiencing intermittent issues with one-way audio and dropped conversations. The manufacturer says the system will work if ping times are less than 50ms.
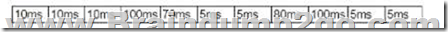
The company has recorded the following ping times:
Which of the following is MOST likely causing the issue?
A. Attenuation
B. Latency
C. VLAN mismatch
D. Jitter
Answer: A
QUESTION 1343
Which of the following security devices would be BEST to use to provide mechanical access control to the MDF/IDF?
A. A smart card
B. A key fob
C. An employee badge
D. A door lock
Answer: B
QUESTION 1344
A network technician is investigating an IP phone that does not register in the VoIP system.
Although it received an IP address, it did not receive the necessary DHCP options.
The information that is needed for the registration is distributes by the DHCP scope All other IP phones are working properly.
Which of the following does the technician need to verify?
A. VLAN mismatch
B. Transceiver mismatch
C. Latency
D. DHCP exhaustion
Answer: A
QUESTION 1345
A network administrator is downloading a large patch that will be uploaded to several enterprise switches simultaneously during the day’s upgrade cycle.
Which of the following should the administrator do to help ensure the upgrade process will be less likely to cause problems with the switches?
A. Confirm the patch’s MD5 hash prior to the upgrade
B. Schedule the switches to reboot after an appropriate amount of time.
C. Download each switch’s current configuration before the upgrade
D. Utilize FTP rather than TFTP to upload the patch
Answer: C
QUESTION 1346
Which of the following is a system that is installed directly on a server’s hardware and abstracts the hardware from any guest machines?
A. Storage array
B. Type 1 hypervisor
C. Virtual machine
D. Guest QS
Answer: A
QUESTION 1347
A city has hired a new employee who needs to be able to work when traveling at home and at the municipal sourcing of a neighboring city that snares services. The employee is issued a laptop, and a technician needs to train the employee on the appropriate solutions for secure access to the network from all the possible locations. On which of the following solutions would the technician MOST likely train the employee?
A. Site-to-site VPNs between the two city locations and client-to-site software on the employee’s laptop tor all other remote access
B. Client-to-site VPNs between the travel locations and site-to-site software on the employee’s laptop for all other remote access
C. Client-to-site VPNs between the two city locations and site-to-site software on the employee’s laptop for all other remote access
D. Site-to-site VPNs between the home and city locations and site-to-site software on the employee’s laptop for all other remote access
Answer: A
QUESTION 1348
An organization with one core and five distribution switches is transitioning from a star to a full-mesh topology. Which of the following is the number of additional network connections needed?
A. 5
B. 7
C. 10
D. 15
Answer: A
QUESTION 1349
Given the following output:
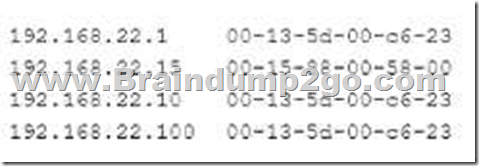
Which of the following attacks is this MOST likely an example of?
A. ARP poisoning
B. VLAN hopping
C. Rogue access point
D. Amplified DoS
Answer: A
QUESTION 1350
An organization wants to implement a method of centrally managing logins to network services. Which of the following protocols should the organization use to allow for authentication, authorization and auditing?
A. MS-CHAP
B. RADIUS
C. LDAPS
D. RSTP
Answer: A
QUESTION 1351
A company wants to implement a large number of WAPs throughout its building and allow users to be able to move around the building without dropping their connections.
Which of the following pieces of equipment would be able to handle this requirement?
A. A VPN concentrator
B. A load balancer
C. A wireless controller
D. A RADIUS server
Answer: A
QUESTION 1352
A network technician is investigating an issue with a desktop that is not connecting to the network. The desktop was connecting successfully the previous day, and no changes were made to the environment. The technician locates the switchport where the device is connected and observes the LED status light on the switchport is not lit even though the desktop is turned on. Other devices that arc plugged into the switch are connecting to the network successfully.
Which of the following is MOST likely the cause of the desktop not connecting?
A. Transceiver mismatch
B. VLAN mismatch
C. Port security
D. Damaged cable
E. Duplex mismatch
Answer: C
QUESTION 1353
A corporation has a critical system that would cause unrecoverable damage to the brand if it was taken offline. Which of the following disaster recovery solutions should the corporation implement?
A. Full backups
B. Load balancing
C. Hot site
D. Snapshots
Answer: C
QUESTION 1354
Which of the following protocol types describes secure communication on port 443?
A. ICMP
B. UDP
C. TCP
D. IP
Answer: C
QUESTION 1355
A local firm has hired a consulting company to clean up its IT infrastructure.
The consulting company notices remote printing is accomplished by port forwarding via publicly accessible IPs through the firm’s firewall.
Which of the following would be the MOST appropriate way to enable secure remote printing?
A. SSH
B. VPN
C. Telnet
D. SSL
Answer: A
Resources From:
1.2021 Latest Braindump2go N10-007 Exam Dumps (PDF & VCE) Free Share:
https://www.braindump2go.com/n10-007.html
2.2021 Latest Braindump2go N10-007 PDF and N10-007 VCE Dumps Free Share:
https://drive.google.com/drive/folders/1Um9XMy881xQGwunqPhEhCGg411Rwh3x9?usp=sharing
3.2021 Free Braindump2go N10-007 Exam Questions Download:
https://www.braindump2go.com/free-online-pdf/N10-007-PDF-Dumps(1355-1372).pdf
https://www.braindump2go.com/free-online-pdf/N10-007-VCE-Dumps(1334-1354).pdf
Free Resources from Braindump2go,We Devoted to Helping You 100% Pass All Exams!